Safely detonate suspicious files, URLs, hashes, and QR codes inside the ZeroFox platform to validate threats, extract intelligence, and generate evidence that accelerates takedowns.
Security teams encounter suspicious files, payloads, and links every day across alerts, investigations, and dark web collection. But they can't act until they know whether the content is actually malicious. Without integrated analysis, teams lose investigation context bouncing between disconnected tools and delay the takedown actions that stop real harm.
ZeroFox Malware Sandboxing embeds multi-engine analysis directly into those workflows so disruption starts with evidence, not guesswork.

ZeroFox Malware Sandboxing enables security teams to submit suspicious files, URLs, hashes, and QR codes for isolated analysis directly inside the ZeroFox platform. Submissions run through multi-engine static scanning, behavioral triage, and deep CAPE analysis to deliver high-confidence verdicts, extracted indicators of compromise, and behavioral reports.

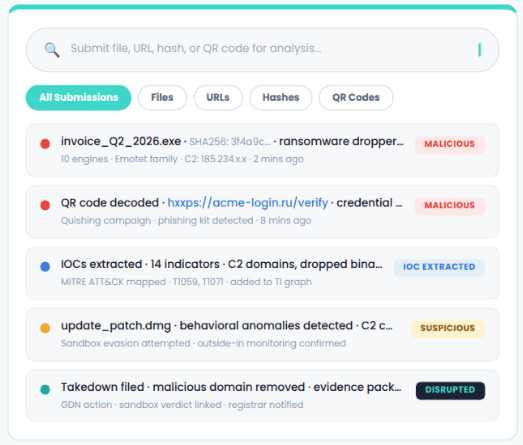

Safely detonate suspicious files and URLs in an isolated environment. Multi-engine detection delivers high-confidence verdicts on whether content is malicious.

Threat validation happens directly inside ZeroFox, eliminating tool-switching and preserving full evidence chain integrity.

Sandbox results generate the supporting evidence needed to justify takedowns against malicious infrastructure, impersonation sites, and phishing campaigns.

IOCs extracted during analysis enrich investigations with behavioral context, C2 infrastructure, dropped files, and MITRE ATT&CK technique mapping.

Automatically decode and detonate QR code URLs and submit file hashes for instant verdict lookup before analysts interact with content.
Your attack surface is expanding, and adversaries are moving faster than ever. GenAI lowers the barrier to entry. Geopolitics fuels motivation. Dark web markets scale opportunity.